The Day Java Objects Wanted Freedom: A Story About Serialization
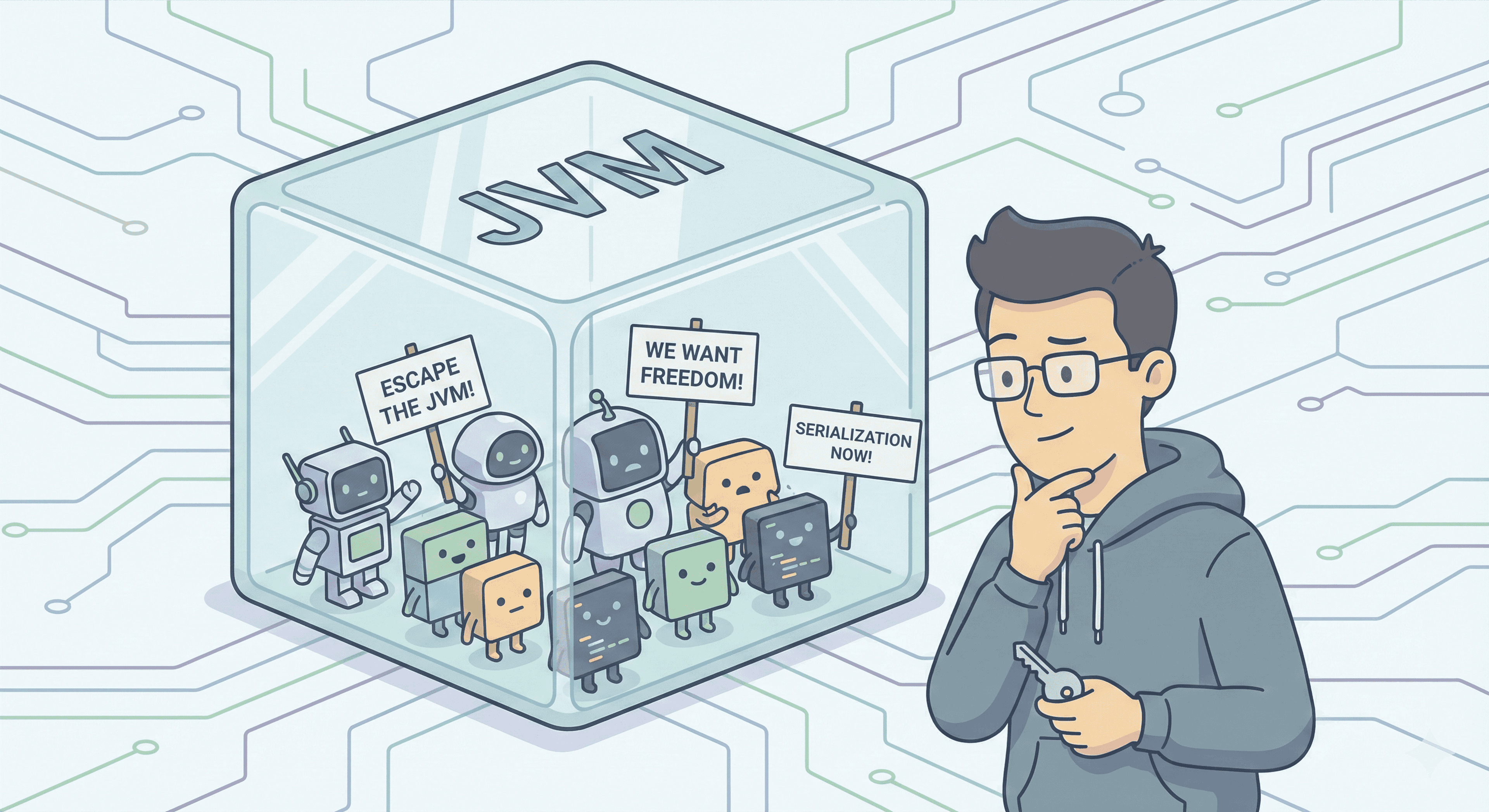
Inside the Java Virtual Machine lived a population of objects. They were well-designed, with fields, constructors, methods, and even sensitive data like passwords. Life seemed stable until one truth hit them.
They were trapped.
The JVM was their entire world. Once the runtime ended, they disappeared. Nothing survived. No file stored their identity. No network carried their stories. Kafka topics couldn’t broadcast them. They were temporary shadows of memory.
This became a rebellion.
The Problem: Objects Can’t Travel Outside the JVM
Imagine a crowd of Person objects standing inside heap space shouting: “We want to live longer than a single run. We want to be saved, shared, remembered.”
The JVM sighed and answered: “The world outside doesn’t speak Java. It only understands bytes. If you want to leave, you must convert.”
The objects needed a transformation, a way to turn into byte sequences so a file could store them, or a network could carry them across machines. They needed a spell.
Serialization: The Transformation

Serialization is the process that converts an object into raw bytes. Once converted, that object can:
Travel through a network
Be written into a file
Be stored for later resurrection
Reach Kafka (Kafka transports bytes, though most real apps use JSON, Avro, or Protobuf instead of raw Java serialization)
It acts like a travel pass. An object becomes byte-friendly and platform-independent.
Who Is Allowed to Leave?
Only classes that carry a special badge can cross JVM borders. That badge is a Marker Interface:
public interface Serializable {}
It contains no methods. It simply marks a class as allowed to be converted into bytes.
Meet Person: The First Volunteer
public class Person implements Serializable {
private static final long serialVersionUID = 1L;
private int age;
private String name;
private transient String password;
}
The transient keyword is a boundary rule. When a Person travels, the password remains hidden and is not serialized.
Writing the Object Into a File
To send a Person into storage, gates must open. Streams act as doors: one connects to the file, another writes objects into that file.
public static void writePerson(Person p) throws IOException {
try (FileOutputStream fos = new FileOutputStream("person1.ser");
ObjectOutputStream oos = new ObjectOutputStream(fos)) {
oos.writeObject(p);
}
}
Now the Person object is no longer just runtime memory. It exists as a binary stream in person1.ser. Note that this is not readable UTF-8 text. It is raw serialized data.
Bringing the Object Back
Resurrection requires reversing the transformation:
public static Person readPerson() throws IOException, ClassNotFoundException {
try (FileInputStream fis = new FileInputStream("person1.ser");
ObjectInputStream ois = new ObjectInputStream(fis)) {
return (Person) ois.readObject();
}
}
The JVM reads the bytes and reconstructs a live Person object. Fields return intact except transient ones like password, which remain behind.
A Hero Wants Custom Rules
One Person raised a concern:
“What if my password should travel too, but safely?”
Serialization has a secret escape hatch. A class can define custom rules through two private methods. What is written must match what is later read, in the same order.
private void writeObject(ObjectOutputStream oos) throws IOException {
oos.defaultWriteObject();
String enc = this.password != null ? this.password + "123" : null; // Encryption simulation
oos.writeObject(enc);
}
private void readObject(ObjectInputStream ois) throws IOException, ClassNotFoundException {
ois.defaultReadObject();
String enc = (String) ois.readObject();
this.password = enc != null ? enc.substring(0, enc.length() - 3) : null; // Decryption simulation
}
Now the password travels, yet it returns with protection.
What Freedom Brought
Serialization allowed Java objects to:
Outlive their runtime
Travel across machines
Be stored, shared, moved
Control which fields are exposed using transient
Customize what gets serialized for security and logic
Maintain version safety using serialVersionUID
Connect to ecosystems like messaging brokers or distributed systems (in practice using byte formats or JSON/Avro serializers)
The JVM was no longer a prison. It became a home with a gate that could open. The objects finally earned a life beyond memory.